You probably have heard of the SolarWinds hack which was published on 14 December 2020. In short, it appears as if Russian state-sponsored hackers have breached the software of SolarWinds, a supplier to 278,000 clients worldwide, amongst them Microsoft and all branches of the US government. The hackers were able to install a back door that allowed them to look at their victim’s computers and files at will, thus enabling them to get access to potential government secrets (very valuable) or the source code of Microsoft Windows (worthless).
From an ESG perspective, I have said before that ESG is probably not enough and that technology risks, especially in the area of data security and data privacy need to be included as well. Funnily, if you look at the materiality map of SASB, the ESG disclosure framework, you will find that ESG investors have paid attention to these data and technology risks for a long time (at least if they took their job seriously). Data security and data privacy is material input in many different sectors ranging from obvious sectors like technology, healthcare, and financials, to food producers and distributors as well as advertising and marketing companies.
It is notable that one of the key lessons of the data breach discussed in the media is the need to ensure your supply chain has the same security standards as your company does. Otherwise, you look pretty stupid if your ironclad security is breached because one of your suppliers is hacked.
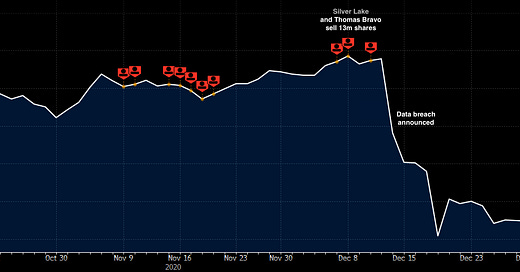
Insider trading around SolarWinds cybersecurity breach announcement
Source: Bloomberg
But the other thing that got me riled up about the SolarWinds breach is that as if by a miracle, a week before the breach was announced two of the company’s largest shareholders, Silver Lake and Thomas Bravo sold more than 13 million shares worth about $300m. These were not scheduled sales but came out of nothing. Insider trading? That is for the SEC to decide who has started investigations.
At first, I was outraged by these trades but then I saw a new study by Andy Naranjo and Svetlana Petrova. They investigated many cybersecurity breaches in the United States and showed that options trading volume by company insiders is elevated in the 20 trading days before a breach is publicly announced. The options that are traded are predominantly put options or bearish call option strategies, not bullish bets on the stock. Of course, if you want to prove that this is insider trading, you need to show that the insiders knew about the data breach before they sold their shares. And that is usually impossible to do. But one might seriously wonder why there is a systematic increase of insider selling in the four weeks before a cybersecurity breach is announced by a company.




Cyber security play is so important as code gets distributed in n everything and everywhere.